Deep in the shadowy corners of the internet lurks a hidden world known as DeDe4D. This infamous platform has become a haven for malicious actors, where they trade illicit goods and data. Users navigate this {digital{ realm using anonymous identities, making it a breeding ground for cybercrime. DeDe4D is notorious for its sale of stolen credentials, weapons, and black market goods. Law enforcement agencies worldwide are struggling to understand and dismantle this complex network before it inflicts further harm.
???? The Deadly Code: Unveiling DeDe4D's Malware Arsenal ????
The shadowy cybercriminal group The DeDe4Ds has been relentlessly churning out a extensive arsenal of wicked code. Their latest tools are designed to destroy critical systems, leaving behind a trail of devastation. Security professionals worldwide are racing to expose the group's strategies, hoping to mitigate the spread of this deadly threat.
DeDe4D has become notorious for its sophisticated malware, which can erase information with alarming speed. Their schemes often target financial institutions, causing significant damage. The group's goal remains unclear, but their viciousness is undeniable.
- Major revelations about DeDe4D's malware include:
- Unique identifiers
- Control over infected systems
- Data exfiltration techniques
????️♀️ Tracking the Trail: A Deep Dive into DeDe4D's Operations ????️♀️
Deep in the shadowy corners of the cyber realm, a notorious group known as DeDe4D operates. These clandestine activities have attracted the attention of investigators worldwide, who are desperately trying to expose their intricate web of operations.
From leaking sensitive information to perpetrating large-scale attacks, DeDe4D has established itself as a major threat. They|'s motives remain obscure, fueling speculation about whom ultimate goals.
A dedicated team of cybersecurity experts is diligently examining vast amounts of data, attempting to piece together the puzzle of DeDe4D's operations. Their investigation get more info involves following digital footprints, recognizing patterns in their activities, and working with|with international agencies. The goal is to neutralize DeDe4D's influence and protect critical infrastructure from future attacks.
Understanding the inner workings of this complex organization is a challenging task, but one that is crucial for maintaining cybersecurity in today's interconnected world.
???? DeDe4d's Ascension and Demise: A Chronicle of Cybercrime ????
DeDe4d, the infamous cybercriminal mastermind, rose to prominence in the early 2010s. Known for his ruthless attacks on high-profile targets, DeDe4d quickly became known for his skill in exploiting weaknesses. His sophisticated methods made him a thorn for law enforcement, who were often left behind with his ever-evolving tools.
Alas, DeDe4d's reign lasted only in 2019. His collapse was a result of a combination of factors, including a tip from a rival hacker by law enforcement. DeDe4d's legacy remains controversial, with some hailing him as a brilliant but unscrupulous innovator.
???? The Price of Silence: Victims Speak Out Against DeDe4d ????
For months the silence was deafening. Victims of her actions were trapped in a world of shame, unable to find their voice. But now, finally, they are {breakingthe chains, demanding revenge for the wrongs inflicted upon them.
- An anonymous voice shared their heartbreaking experience, revealing the brutality of DeDe4d's control.
- His confession sent shockwaves through the community, provoking a wave of outrage.
- He is now facing the full force of their deeds, as victims unite to ensure that this never happens again.
????️ Defending Against DeDe4d: Cybersecurity Strategies for a Safer Future ????️
As cyber threats evolve at an alarming pace, staying ahead of malicious actors like DeDe4d is paramount. This sophisticated malware poses a significant threat to organizations and individuals alike, employing sophisticated techniques to infiltrate systems. Implementing robust cybersecurity strategies is crucial for mitigating these risks and safeguarding sensitive data.
To begin with, it's imperative to harden network security by adopting firewalls, intrusion detection systems (IDS), and other security protocols. Regularly update software and operating systems to mitigate known vulnerabilities. User education and awareness are also essential. Training employees to recognize phishing attempts, social engineering tactics, and other common threats can substantially reduce the risk of successful attacks.
Furthermore, consider implementing multi-factor authentication (MFA) to add an extra layer of defense. MFA requires users to provide multiple forms of proof before gaining access to sensitive systems or data. Regularly perform security audits and penetration testing to uncover weaknesses in your defenses. By taking these proactive steps, organizations can successfully defend against DeDe4d and other emerging threats.
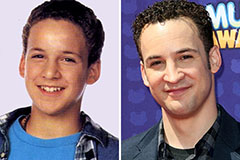 Ben Savage Then & Now!
Ben Savage Then & Now! Jenna Von Oy Then & Now!
Jenna Von Oy Then & Now! Bo Derek Then & Now!
Bo Derek Then & Now! Brooke Shields Then & Now!
Brooke Shields Then & Now! Christy Canyon Then & Now!
Christy Canyon Then & Now!